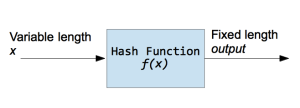
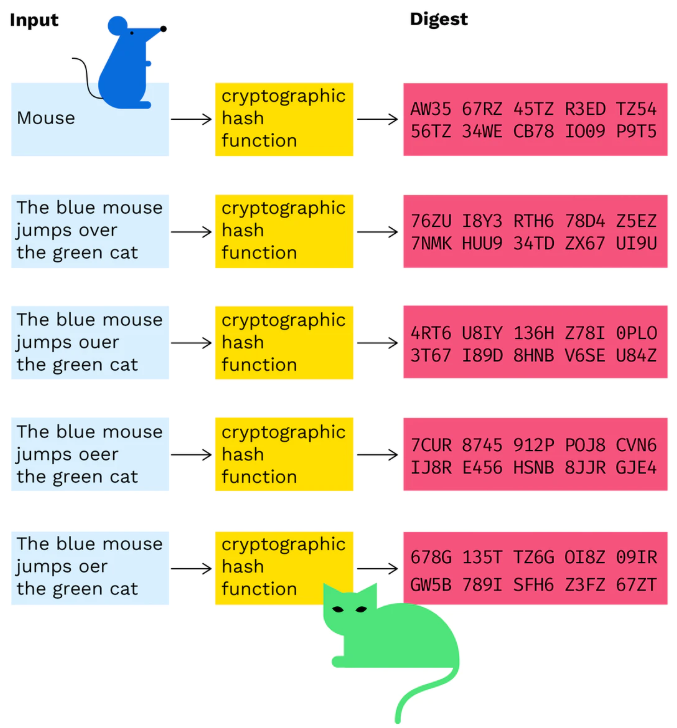
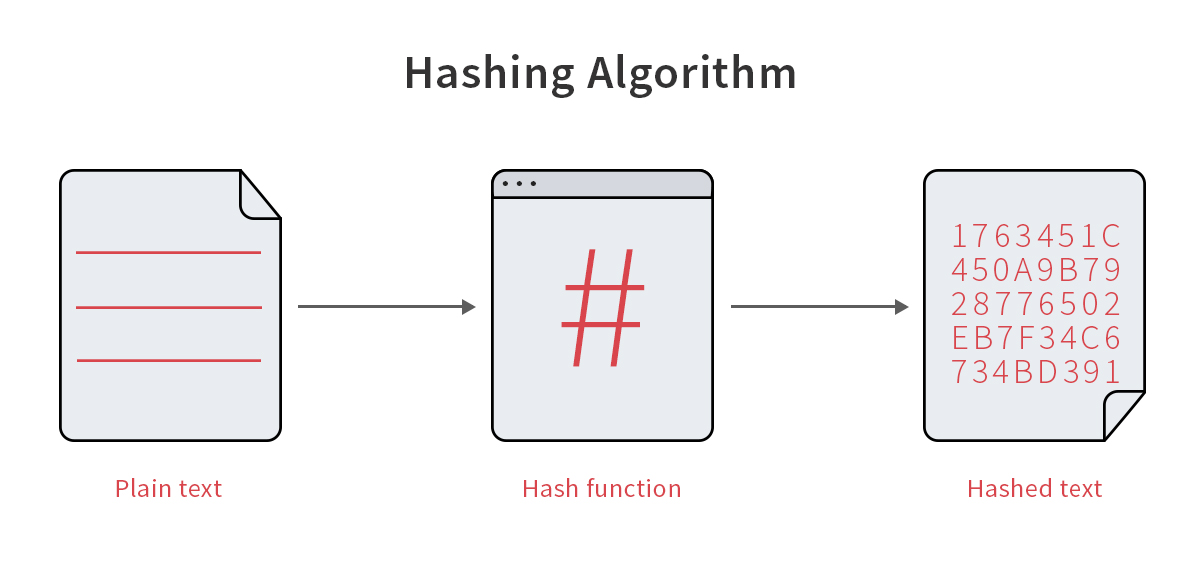
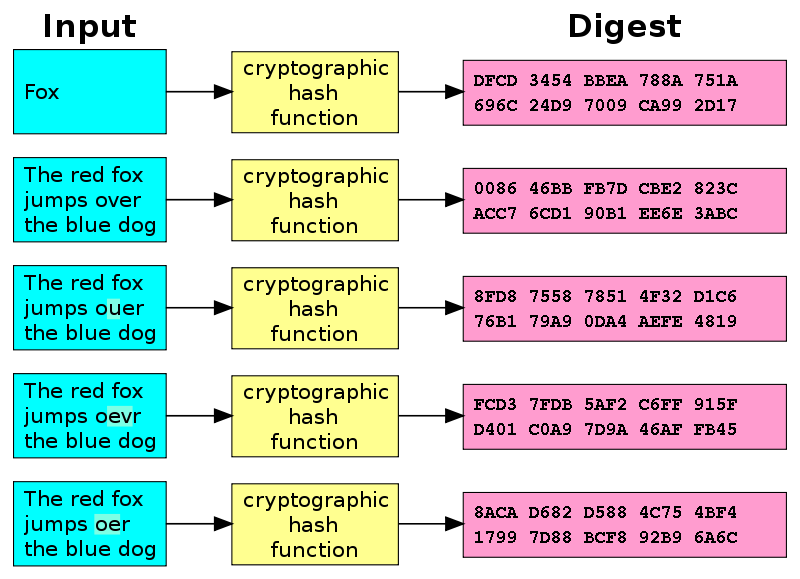
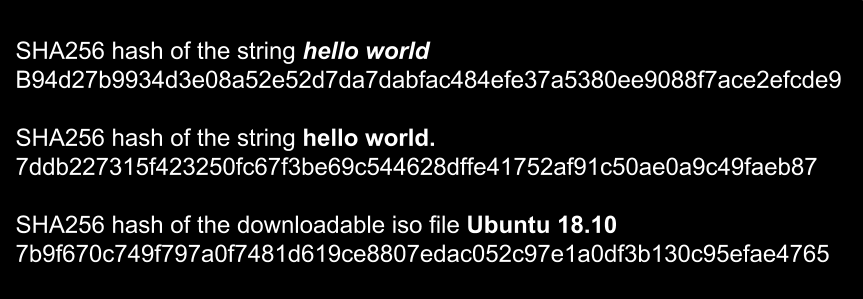
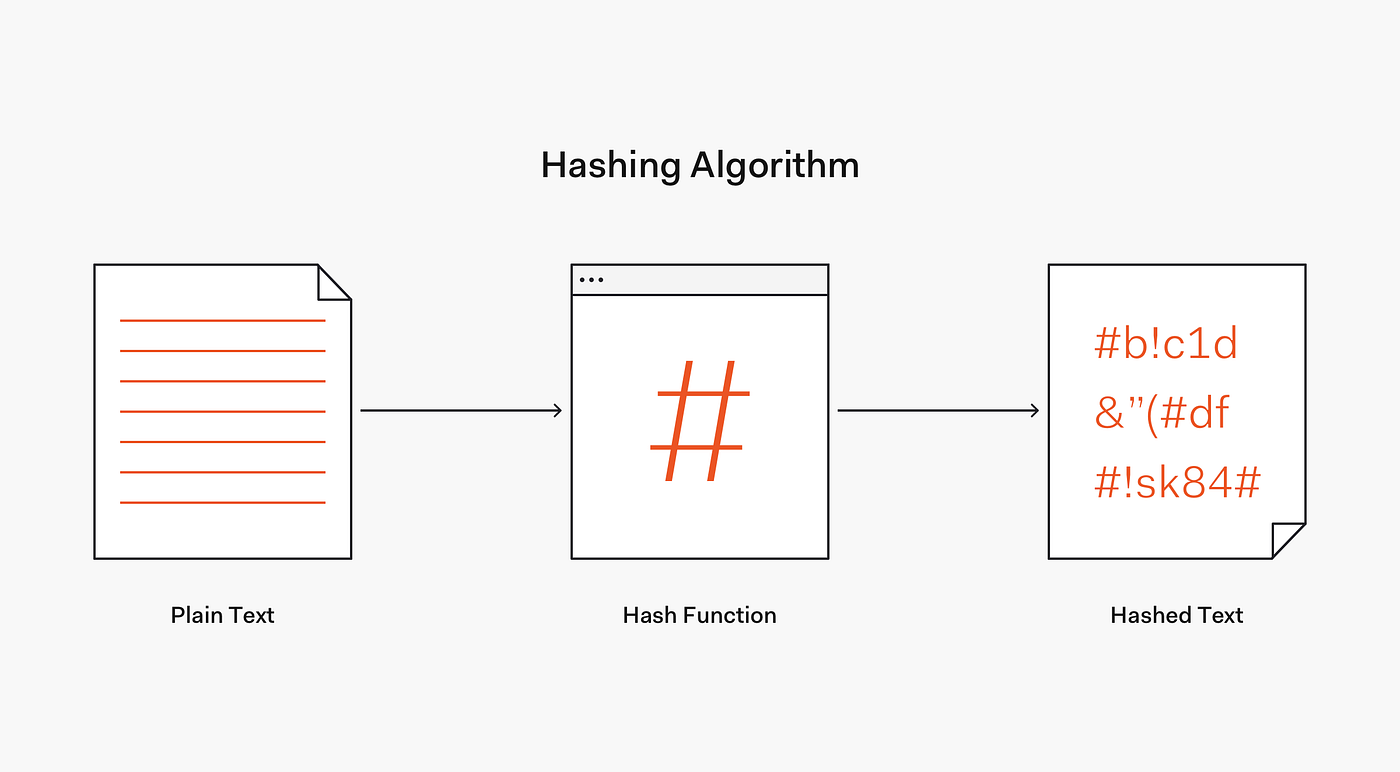
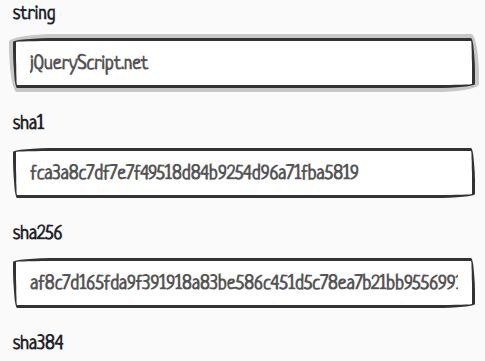
A: hash functions convert data into fixed-length strings (hashes). B:... | Download Scientific Diagram
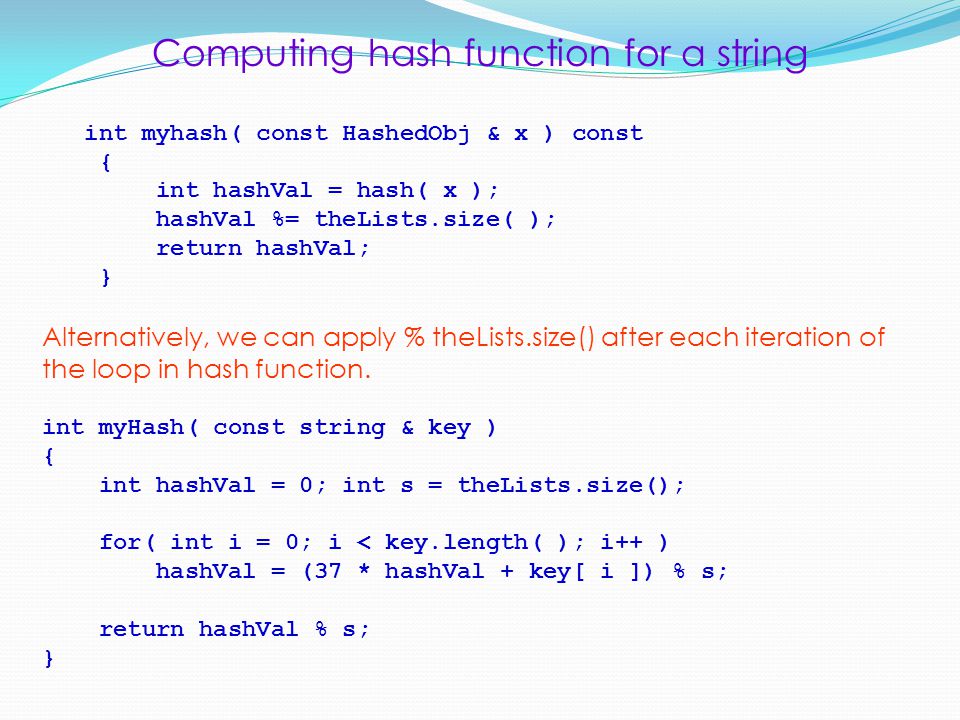
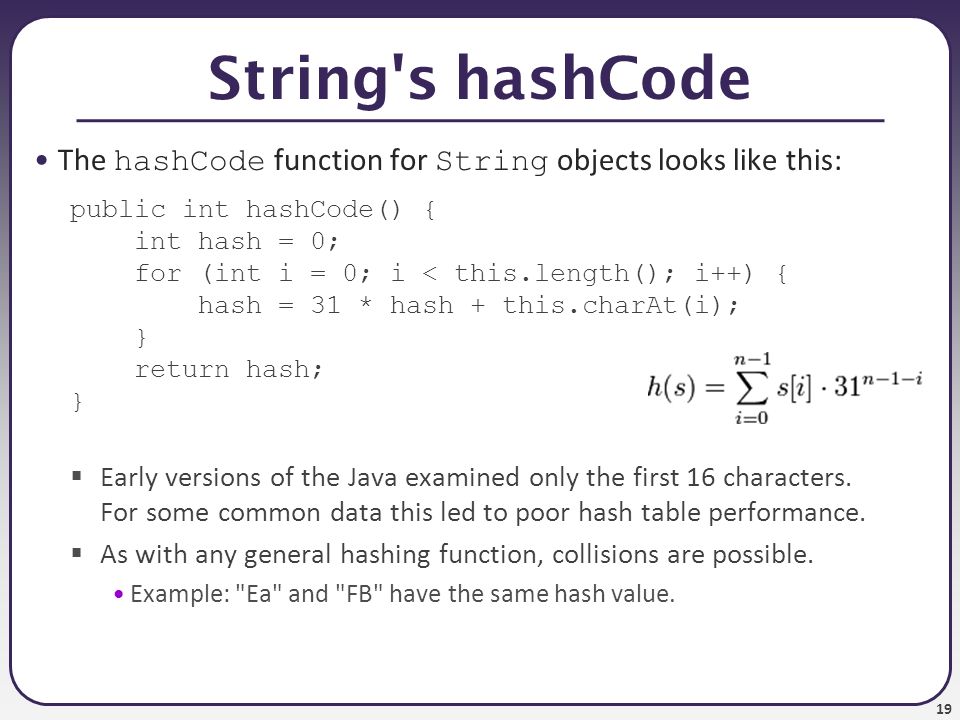
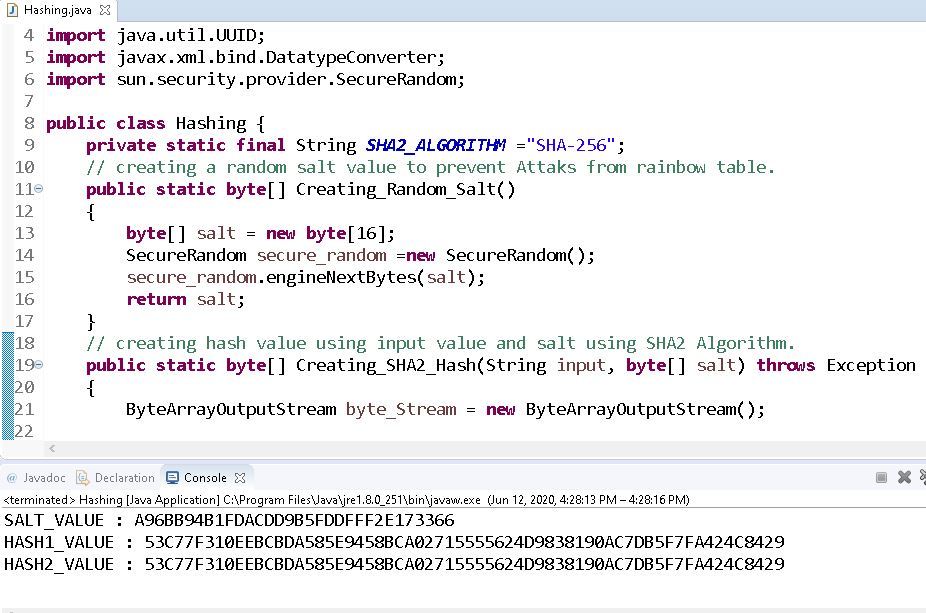
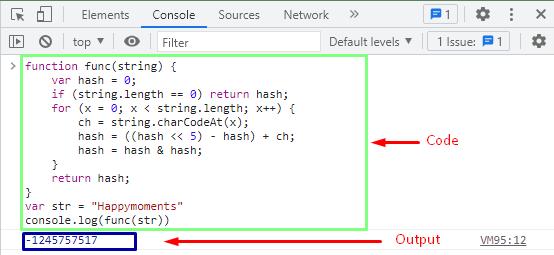
L. Grewe. Computing hash function for a string Horner's rule: (( … (a 0 x + a 1 ) x + a 2 ) x + … + a n-2 )x + a n-1 ) int hash( const string & key ) - ppt download